Intelligent threats bypass standard security. We deliver continuous behavioral monitoring and automated containment with expert incident response.
Cloud-native architecture scaling from 50 to 50,000 endpoints seamlessly.

On the hunt.
Survival of the Fastest
To stay ahead you must:
DETECT IN
1 MIN
Investigate in
10 MIN
Respond In
60 MIN
Customized indicators of attack and compromise developed across 500,000+ users detect threats standard CrowdStrike configurations miss.
Expert-configured containment rules instantly quarantine compromised endpoints while preserving forensic evidence for investigation.

Frequently Asked Questions
Endpoints are any devices that connect to your network including laptops, desktops, smartphones, tablets, servers, and IoT devices. Each endpoint represents a potential entry point for cyber threats, making comprehensive endpoint protection critical for organizational security. Modern workforces using remote devices and BYOD policies dramatically expand your endpoint attack surface. Our cybersecurity architecture secures all endpoint types with military-grade protection.
Our endpoint security platform leverages the same detection technologies trusted by defense contractors and government agencies, including advanced behavioral analytics, zero-trust verification, and automated threat response. We implement NIST security frameworks, maintain security clearances, and deploy enterprise-grade tools that meet the most stringent security requirements. Our cross-platform protection extends military-grade security across your entire digital infrastructure, including messaging and social media.
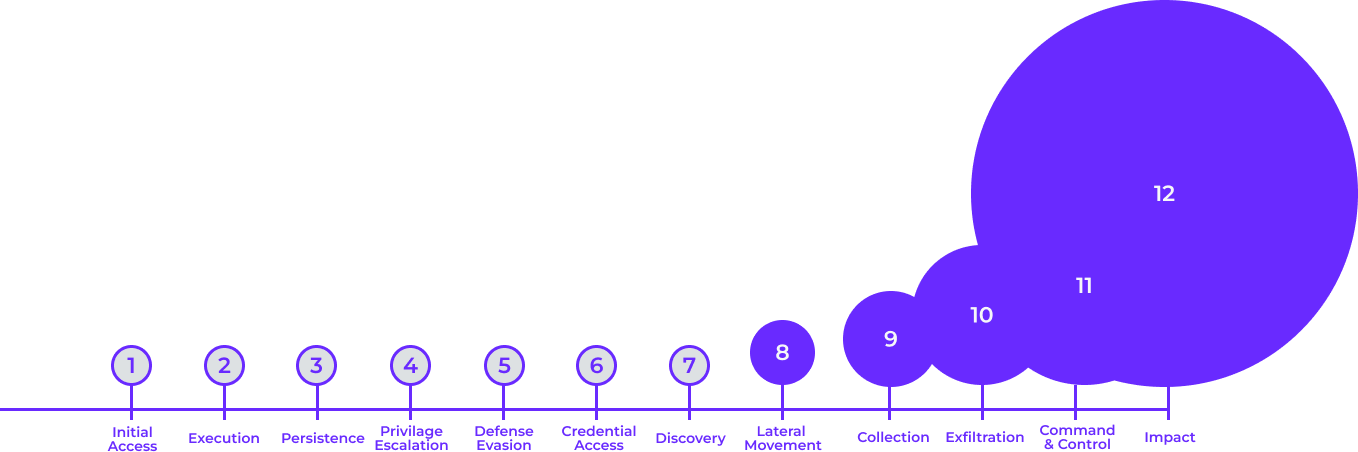
Our endpoint security platform delivers sub-minute threat detection with automated containment capabilities that isolate compromised devices within 15 minutes. Advanced behavioral analytics identify suspicious activity before traditional signature-based tools, while automated response workflows prevent lateral movement across your network. Real-time monitoring ensures threats are contained before they can spread or cause significant damage. Our cybersecurity team provides 24/7 monitoring and incident response.
Remote and hybrid workforces require comprehensive endpoint protection that works regardless of network location, including VPN-independent security, cloud-based management, and protection for personal devices accessing corporate resources. We provide consistent security policies across all devices, secure remote access capabilities, and compliance monitoring for distributed teams. Our managed IT platform secures distributed workforces without compromising productivity.
EDR (Endpoint Detection and Response) continuously monitors endpoint activities, creating detailed behavioral baselines and identifying anomalies that indicate sophisticated attacks. Our platform correlates endpoint data with network intelligence, providing comprehensive visibility into attack patterns and enabling proactive threat hunting. Advanced machine learning algorithms detect zero-day threats and living-off-the-land attacks that bypass traditional security tools. Our cross-platform protection delivers enterprise-grade EDR capabilities.
Comprehensive endpoint security addresses multiple compliance frameworks including CMMC, NIST, HIPAA, PCI DSS, and SOX requirements. Our platform provides automated compliance reporting, audit trail documentation, and policy enforcement capabilities that simplify regulatory compliance. Endpoint protection is particularly critical for organizations handling sensitive data or operating in regulated industries. Our cybersecurity solutions ensure your endpoints meet all regulatory requirements.
IoT devices and non-traditional endpoints require specialized security approaches including network segmentation, device discovery and classification, and behavioral monitoring for devices that cannot run traditional security agents. Our platform provides comprehensive visibility into all connected devices, implements appropriate access controls, and monitors for suspicious activity across your entire IoT infrastructure. Our managed IT services extend protection to every connected device in your environment.
Our managed endpoint security operates on behavioral analytics and sub-15-minute automated response, while traditional IT security relies on signature-based detection that misses 67% of advanced threats targeting remote workforces. Managed endpoint protection transforms unpredictable breach costs averaging $4.44 million into fixed operational expenses through 24/7 SOC monitoring and proactive threat hunting. Our platform combines machine learning detection with human analysis to identify zero-day exploits and living-off-the-land attacks that bypass conventional antivirus solutions. Our managed services provide the enterprise-grade protection typically reserved for Fortune 500 companies at a fraction of traditional security operations center costs.
Our cloud-native architecture eliminates the infrastructure bottlenecks that plague traditional on-premises security solutions, automatically scaling across Windows, macOS, iOS, Android, and IoT endpoints without requiring additional hardware investments. Managed endpoint security services deliver centralized policy management that adapts security baselines to device capabilities while maintaining unified compliance reporting across thousands of devices. Our platform supports rapid business growth, merger and acquisition activities, and seasonal workforce expansion through automated provisioning workflows that deploy consistent security policies in minutes rather than weeks. Cross-platform security ensures zero-trust principles apply consistently across your entire device ecosystem regardless of location or network connection.
Our endpoint security platform automates compliance evidence collection and continuous assessment across CMMC, NIST, HIPAA, and SOX frameworks simultaneously, with specialized expertise in CMMC Level 2 and 3 requirements for defense contractors. Compliance automation services provide real-time policy enforcement, detailed audit trail documentation, and automated remediation that addresses device encryption, access management, and incident response capabilities without manual intervention. Our security clearance-holding team understands the unique challenges defense contractors face, providing the specialized knowledge required to maintain continuous compliance rather than just passing point-in-time assessments. Managed IT compliance services adapt to regulatory changes automatically, ensuring your endpoint security posture evolves with compliance requirements without disrupting business operations.
Our behavioral analytics establish individual device baselines and detect subtle deviations indicating compromise, including fileless malware and living-off-the-land attacks that traditional signature-based solutions miss entirely. Cross-platform threat protection leverages machine learning algorithms that evolve with threat landscapes, identifying zero-day exploits and novel attack patterns within minutes of execution. Our automated response capabilities isolate compromised devices within 15 minutes while preserving forensic evidence for investigation, preventing lateral movement while maintaining business continuity for unaffected systems. Advanced cybersecurity monitoring combines 24/7 SOC oversight with proactive threat hunting to detect advanced persistent threats that remain hidden from conventional security tools.
Microsoft Intune delivers automated security baseline configuration that aligns with NIST, CIS, and Microsoft security recommendations across hundreds of settings, but our implementation expertise ensures these baselines are properly configured for your specific compliance requirements. Microsoft 365 endpoint management includes conditional access integration, application protection policies for personal devices, and real-time compliance monitoring with automated remediation workflows that most organizations struggle to implement effectively. Our Microsoft-certified team configures Intune's zero-trust capabilities to evaluate device risk, location, and behavior patterns before granting resource access through dynamic security boundaries that adapt to changing threat levels. Expert cybersecurity implementation enables custom compliance policies that address industry-specific regulations while maintaining the scalability and manageability that make Intune effective for enterprise environments.
Inc. Magazine's fastest growing leader in Managed Cybersecurity—3 years in a row.
Rapid response times, with around the clock IT support, from Inc. Magazine’s #1 MSSP.
Rapid response times, with around the clock IT support, from Inc. Magazine’s #1 MSSP.