
AI adoption accelerates but creates dangerous blind spots in data protection. We eliminate those gaps.
Microsoft AI interactions stay secure with Ridge Security Lab’s advanced threat protection.
Lock it down.
Netskope inspects web traffic and cloud services with deep context understanding, analyzing transactions in real-time.
Transaction event streaming and user risk scoring enables adaptive access policies based on context in use.
Frequently Asked Questions
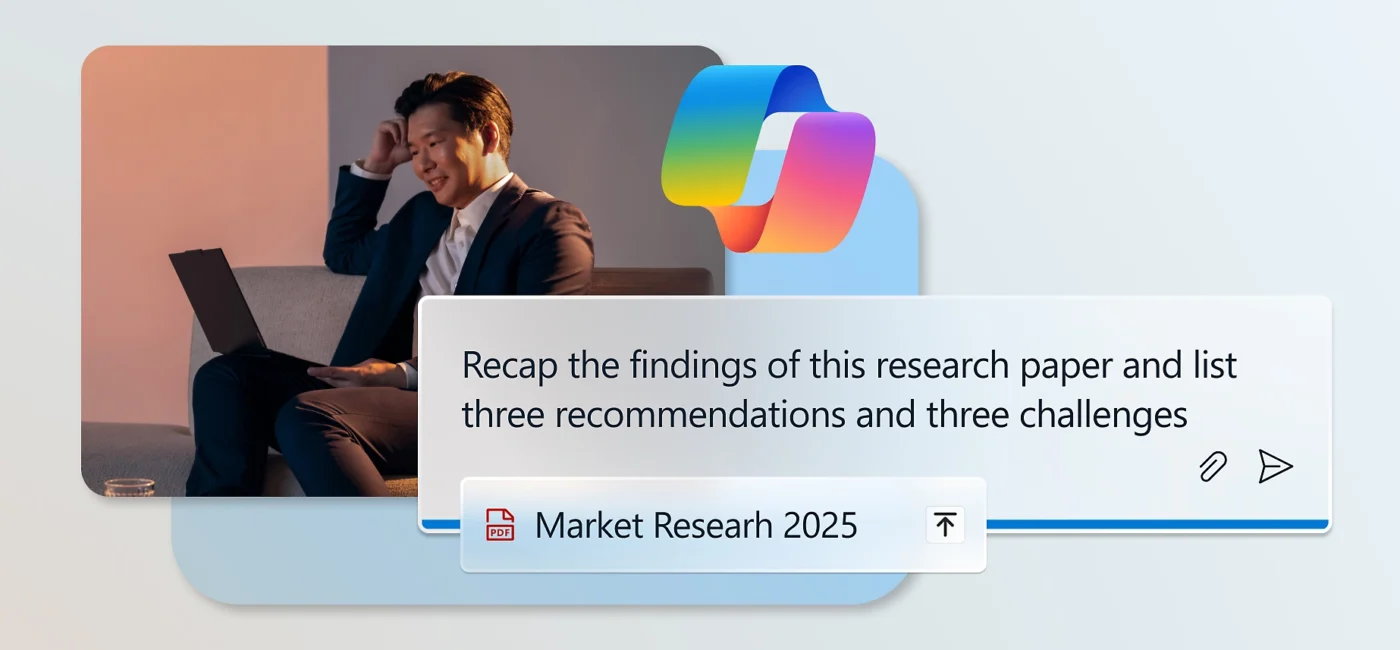
Absolutely. If building AI solutions with Azure Foundry or other models within the Microsoft ecosystem, Purview capabilities apply across all Microsoft workloads. All classification, labeling, and data governance features available with Microsoft 365 Copilot extend to broader Azure components and custom LLM implementations that leverage Microsoft Graph. Our Microsoft security integration covers the complete AI ecosystem.
No, Copilot does not train on organizational data or leak information into the model. Each organization has their own instance of the AI and Large Language Model (LLM). Customer A's LLM is completely separate from Customer B's LLM. Copilot consists of three components: the LLM, semantic index, and Microsoft Graph, but all data stays within the organization's instance and is never used for training purposes. Our Microsoft AI security framework ensures complete data isolation.
The core problem: Microsoft Copilot honors existing SharePoint permissions while dramatically expanding data discovery through AI-powered search and correlation. Minor permission oversights become major Microsoft AI security breaches.
Rather than blocking Microsoft AI deployment, the Cloud Solution Architect recommends systematic Copilot security implementation that enables confident artificial intelligence adoption.
Engage Microsoft 365 administrators including SharePoint, Compliance, and Copilot security teams for comprehensive AI protection coverage.
Define Microsoft AI sensitivity standards by establishing clear Copilot data classification criteria that prevent artificial intelligence overexposure.
Discover Copilot data access patterns using SharePoint Data Access Governance reports to identify Microsoft AI security vulnerabilities.
Prioritize Microsoft AI data protection by securing the most sensitive Copilot-accessible information first through targeted artificial intelligence security controls.
Deploy Microsoft Purview solutions that provide ongoing Copilot security rather than one-time Microsoft AI protection fixes.
AI Agents introduce compliance complexities around data residency, audit trail requirements, and regulatory approval processes. The M365 Copilot API can create data flows that violate industry regulations if not properly configured. Healthcare, financial, and defense organizations face particular compliance challenges with agent-generated content and automated decision-making processes. We address regulatory requirements for AI implementations.
The primary data leakage risks include employees accidentally sharing sensitive information in prompts, Copilot responses containing confidential data from connected systems, and unauthorized data access through poorly configured agent permissions. Code Interpreter functions can expose proprietary algorithms, while CUA (Conversational User Authentication) bypasses may grant excessive access. We prevent data loss across all AI interactions.
The core problem: Microsoft Copilot honors existing SharePoint permissions while dramatically expanding data discovery through AI-powered search and correlation. Minor permission oversights become major Microsoft AI security breaches.
Rather than blocking Microsoft AI deployment, the Cloud Solution Architect recommends systematic Copilot security implementation that enables confident artificial intelligence adoption.
Engage Microsoft 365 administrators including SharePoint, Compliance, and Copilot security teams for comprehensive AI protection coverage.
Define Microsoft AI sensitivity standards by establishing clear Copilot data classification criteria that prevent artificial intelligence overexposure.
Discover Copilot data access patterns using SharePoint Data Access Governance reports to identify Microsoft AI security vulnerabilities.
Prioritize Microsoft AI data protection by securing the most sensitive Copilot-accessible information first through targeted artificial intelligence security controls.
Deploy Microsoft Purview solutions that provide ongoing Copilot security rather than one-time Microsoft AI protection fixes.
Microsoft 365 Copilot and AI Agents create new security risks. The attack vectors include data leakage through prompt injection, oversharing of sensitive information in AI responses, and unauthorized access to organizational data through compromised AI interactions. The Researcher and Analyst agents can inadvertently expose confidential business intelligence if not properly secured. We secure Copilot and identify these vulnerabilities before they become breaches.
https://www.youtube.com/watch?v=rAg64tgoW6UThe core problem: Microsoft Copilot honors existing SharePoint permissions while dramatically expanding data discovery through AI-powered search and correlation. Minor permission oversights become major Microsoft AI security breaches.
Rather than blocking Microsoft AI deployment, the Cloud Solution Architect recommends systematic Copilot security implementation that enables confident artificial intelligence adoption.
Engage Microsoft 365 administrators including SharePoint, Compliance, and Copilot security teams for comprehensive AI protection coverage.
Define Microsoft AI sensitivity standards by establishing clear Copilot data classification criteria that prevent artificial intelligence overexposure.
Discover Copilot data access patterns using SharePoint Data Access Governance reports to identify Microsoft AI security vulnerabilities.
Prioritize Microsoft AI data protection by securing the most sensitive Copilot-accessible information first through targeted artificial intelligence security controls.
Deploy Microsoft Purview solutions that provide ongoing Copilot security rather than one-time Microsoft AI protection fixes.
AI security for SMBs differs from traditional cybersecurity in four critical ways:
Most critically, AI security for SMBs recognizes that 83% of SMBs face increased threats but traditional tools like basic antivirus (used by 68% of SMBs) are inadequate against AI-powered attacks.
Detecting compromised AI security for SMBs requires monitoring for specific warning signs: unexplained network traffic increases (especially to unusual geographic locations indicating data exfiltration), system performance degradation without obvious cause, unusual login attempts or authentication failures, vendor security notifications about your IP address appearing in threat intelligence, alerts from managed security providers about anomalous behavior, and employees reporting unusual system behavior.
The challenge for AI security for SMBs is that AI-powered attacks often operate stealthily—average breach discovery time is 207 days for SMBs without managed security versus 3-6 hours with 24/7 monitoring. If you suspect compromised AI security for SMBs, immediately contact a cybersecurity incident response team rather than investigating internally, as self-investigation may alert attackers or destroy forensic evidence needed for recovery and insurance claims.
Effective AI usage policies are foundational to AI security for SMBs. Your policy should specify:
AI security for SMBs requires these policies that cost $0 to implement but prevent shadow AI usage that caused one 75-employee SMB to lose $6.7M.
Slopsquatting attacks exploit AI hallucinations to compromise AI security for SMBs by weaponizing fake software packages. When developers at SMBs use AI coding assistants like ChatGPT, GitHub Copilot, or Claude, these tools sometimes recommend packages that don't exist—19.7% of AI recommendations according to university research.
Cybercriminals monitor which fake packages AI models consistently hallucinate, then register those package names (like "hipaa-auth-validator" or "mysql-async-connection-pool-pro") and upload malware-laden code. Developers trust the AI recommendation and install the package, compromising AI security for SMBs. This threat specifically targets SMBs because Fortune 500 companies have security teams reviewing dependencies, while SMBs typically don't. Slopsquatting attacks often remain undetected for months at SMBs without 24/7 monitoring.
AI security for SMBs costs significantly less than breach recovery. Industry averages for managed security services range from $36,000-$48,000 annually for SMBs with 10-50 employees, $60,000-$96,000 for SMBs with 50-200 employees, and $96,000-$180,000 for SMBs with 200-500 employees. Compare this to the average AI-powered breach cost of $254,445 for SMBs, with 60% of breached SMBs closing within 6 months.
Real examples show AI security for SMBs preventing catastrophic losses: a 50-employee healthcare SMB lost $3.2M from a slopsquatting attack, a 200-employee manufacturer lost $4.5M from AI-hallucinated malware, and a 75-employee professional services firm lost $6.7M from shadow AI usage. One prevented breach pays for 2-7 years of AI security for SMBs.
AI security for SMBs refers to cybersecurity measures protecting small and medium-sized businesses (10-500 employees) from threats that exploit or are powered by artificial intelligence. This includes slopsquatting attacks where AI tools recommend non-existent software packages (19.7% of AI recommendations), AI-powered phishing with 98% accurate voice cloning, and automated malware that adapts in real-time.
AI security for SMBs matters because 83% of SMBs report AI has increased their threat level, yet 47% have no cybersecurity budget—creating a dangerous gap. Unlike traditional cybersecurity, AI security for SMBs requires governance policies for employee AI tool usage, dependency scanning to catch hallucinated packages, and vendor risk assessments to ensure third parties validate AI-generated code before production deployment.
AI Zero Trust identity verification transforms static authentication into continuous, adaptive security by analyzing user behavior patterns, device posture, access context, and threat intelligence in real-time to assign dynamic trust scores. By 2028, 60% of Zero Trust tools will incorporate AI capabilities including behavioral biometrics (keystroke patterns, mouse movements), anomaly detection, automated policy enforcement, and predictive threat identification—enabling organizations to detect compromised credentials before attackers can exploit them.
AI-powered identity verification continuously monitors sessions rather than just validating at login, automatically adjusting access permissions when detecting unusual activities like impossible travel, abnormal data access patterns, or suspicious application usage. This adaptive approach reduces false positives while catching sophisticated attacks that bypass traditional MFA. Ridge IT's AI-enhanced Zero Trust implementations leverage machine learning to create unique behavioral profiles for each user, automatically blocking access when deviations occur.
Automated threat response fundamentally changes how organizations contain cyberattacks, compressing response timelines from hours or days to seconds or minutes. When AI security systems detect threats, automated threat response capabilities initiate a coordinated sequence of protective actions that neutralize attacks before they accomplish their objectives.
The automated threat response process follows a carefully orchestrated sequence: immediate alert generation notifies security teams with clear threat descriptions; automatic system isolation disconnects affected endpoints to prevent lateral movement; forensic data collection captures memory dumps, process execution chains, and network logs; and automated remediation quarantines malicious files, terminates suspicious processes, and rolls back malicious changes.
Throughout this process, automated threat response provides user-friendly visibility through dashboards showing complete attack scope, affected systems, response actions taken automatically, current containment status, and recommended next steps.
Ridge IT Cyber has documented numerous cases demonstrating effectiveness. During a recent ransomware attempt, our AI detection identified the initial compromise within 38 seconds. Automated threat response immediately isolated the affected endpoint and prevented any data encryption—total response time under 3 minutes. Traditional security requiring manual investigation would have taken 30-60 minutes minimum, allowing ransomware to encrypt critical business data.
Organizations can implement AI security remarkably quickly—Ridge IT Cyber typically achieves full protection within 72 hours from contract signature to active threat monitoring. Modern cloud-based AI security platforms eliminate lengthy hardware procurement and installation cycles, enabling rapid deployment that provides immediate protection against active threats.
The ability to implement AI security this quickly stems from cloud-native architecture: no on-premises hardware installation, no network architecture changes requiring outage windows, lightweight endpoint agents that deploy via existing management tools, and automated configuration that eliminates manual setup. These advantages mean security teams can deploy AI security across thousands of endpoints in hours rather than weeks.
When you implement AI security with Ridge IT, the deployment follows a proven rapid timeline: Day 1 involves planning and credential setup; Days 1-2 include automated agent deployment across endpoints; Day 3 covers activation, monitoring, and team training. Behavioral baselines reach maturity within the first week as AI establishes normal patterns for users, devices, and applications.
For organizations requiring CMMC compliance or specific regulatory frameworks, Ridge IT can implement AI security foundational controls within 72 hours while building comprehensive compliance programs over subsequent months. Contact us to discuss your specific timeline requirements and how quickly we can establish AI-powered protection.
Yes, organizations absolutely need human security analysts even with automated security systems—AI augments human expertise but cannot replace strategic thinking, complex decision-making, and business context. The optimal security model combines automated security for continuous monitoring and rapid response with human analysts for strategic oversight and critical decisions.
Automated security excels at capabilities humans cannot match: processing massive data volumes 24/7 without fatigue, analyzing millions of security events per second, identifying subtle patterns invisible to human observation, and executing rapid automated responses within seconds. However, automated security has limitations that require human intelligence: complex threat investigation requiring business context, strategic security planning aligned with business objectives, policy creation balancing security with usability, and critical decisions during major incidents.
The cybersecurity skills shortage means automated security helps scarce human talent focus on high-value activities rather than repetitive tasks. Instead of manually reviewing thousands of security logs, human analysts receive AI-curated alerts with clear threat descriptions and recommended responses.
Ridge IT Cyber's managed security operations demonstrate this partnership: AI-powered platforms handle continuous monitoring and automated containment, while Tampa-based security analysts with federal clearances provide complex investigation, strategic roadmap development, and incident command during major events. For small businesses, partnering with an MSSP provides both automated security technology and expert human analysts at a fraction of in-house costs.
AI threat detection delivers measurable, verifiable results that fundamentally improve cybersecurity outcomes—this is not marketing hype but documented fact. Leading AI threat detection platforms like CrowdStrike process over 30 trillion security events weekly using machine learning algorithms that achieve a documented 99.9% breach prevention rate. The technology enables detection of zero-day threats with no known signatures, automates investigations that would take human analysts hours, and responds to threats in seconds.
The effectiveness of AI threat detection is measurable through specific capabilities: behavioral anomaly detection identifies threats based on what they do, not what they look like; predictive threat intelligence forecasts which vulnerabilities attackers will target next; automated threat hunting proactively searches for indicators of compromise; and sub-minute detection timelines compress the window attackers have to accomplish objectives.
However, many vendors misuse "AI" as a marketing term for simple automation or basic machine learning. True AI threat detection involves machine learning models that improve continuously, behavioral analytics that establish baselines and detect deviations, and automated decision-making based on risk scoring and context.
When evaluating AI threat detection solutions, look for documented threat prevention rates from independent validation, transparent methodologies, published case studies, and global threat intelligence integration. Ridge IT's managed security services leverage only best-in-class AI threat detection platforms with proven track records demonstrating 98.7% threat prevention across 500,000+ protected users.
AI technology can reduce security false positives by 70-80% through behavioral analytics and contextual awareness that static rule-based systems cannot achieve. False positives—legitimate activities incorrectly flagged as threats—create alert fatigue that overwhelms security teams, causing them to ignore or miss actual attacks buried in thousands of irrelevant warnings.
AI-powered platforms reduce security false positives through sophisticated behavioral modeling. Instead of rigid rules, machine learning algorithms learn what "normal" looks like for each user, device, and application. The AI considers multiple contextual factors simultaneously: user role and typical work patterns, time of day and access location, historical behavior and peer group norms, and data sensitivity and business impact. This contextual intelligence prevents false alarms while maintaining high detection accuracy.
Ridge IT Cyber's Microsoft 365 security implementations use Mimecast social graphing that builds detailed communication models for every employee. When business email compromise attacks occur, the AI instantly detects deviations from established baselines—catching sophisticated attacks while ignoring legitimate variations that rule-based systems would incorrectly flag.
The ability to reduce security false positives enables faster incident response. When security analysts trust that AI alerts represent genuine threats, they investigate immediately rather than dismissing notifications. Our managed detection and response services leverage AI platforms that achieve 98%+ alert accuracy, essentially eliminating alert fatigue.
Rapid incident response time is the most critical factor determining whether a cyberattack becomes a minor security event or a catastrophic business disruption. Every second matters—attackers can exfiltrate gigabytes of data, deploy ransomware, or establish backdoors within minutes of initial compromise. This is why Ridge IT Cyber implements the 1-10-60 standard: detect threats in 1 minute, investigate in 10 minutes, and take containment action within 60 minutes.
Achieving rapid incident response time at this level is only possible through AI-powered automation combined with expert human analysis. Traditional security operations centers often take hours or days to investigate security alerts, giving attackers plenty of time to accomplish their objectives. AI-powered platforms compress these timelines dramatically through continuous behavioral monitoring, automatic forensic evidence collection, instant system isolation to prevent lateral movement, and clear threat descriptions for rapid validation.
The business impact of rapid incident response time is measurable. Organizations that contain breaches in less than 200 days save an average of $1.12 million compared to longer response times. Ridge IT has documented cases where our AI detection identified ransomware within 38 seconds and prevented any encryption—total rapid incident response time under 3 minutes from detection to complete containment.
Our 24/7 security operations center combines AI automation with human expertise to consistently achieve these rapid response timelines, preventing breaches rather than merely documenting them after damage occurs.
Yes, small and medium-sized businesses can absolutely afford AI security tools through Managed Security Service Providers (MSSPs) like Ridge IT. Organizations access enterprise-grade AI security tools including 24/7 monitoring, automated threat detection, incident response, and compliance support without building expensive in-house security teams.
The key to affordability is the managed service model. Leading AI security tools like CrowdStrike EDR and XDR platforms typically cost six figures annually when purchased directly. However, MSSPs leverage economies of scale—sharing these tool investments across hundreds of clients—making the same technology accessible to businesses of all sizes at a fraction of the cost.
More importantly, investing in AI security tools costs far less than breach recovery. The average small business data breach now costs $2.5-3.2 million, including regulatory fines, legal fees, customer notification, lost productivity, and reputation damage. Ridge IT clients typically achieve 60% reduction in total security costs through tool consolidation and optimization while dramatically improving protection.
Request a security assessment to understand exactly how AI-powered security fits your budget while eliminating the risk exposure that threatens your business continuity.
AI cyber attacks represent a quantum leap in threat sophistication, fundamentally changing the cybersecurity landscape. While traditional cyberattacks follow predictable patterns that security teams can recognize and block, AI cyber attacks continuously evolve and adapt in real-time, making them exponentially more dangerous and difficult to detect.
The most significant difference is speed and scale. AI cyber attacks automate network reconnaissance, vulnerability exploitation, and lateral movement through systems 24/7 without rest. Research shows that AI cyber attacks using generative AI for phishing achieve 135% higher click-through rates compared to traditional phishing emails, primarily because AI creates perfectly written, personalized messages with zero grammatical errors.
AI cyber attacks also demonstrate unprecedented adaptability. AI-powered malware morphs its code with each infection, evading signature-based detection completely. These attacks analyze defender responses in real-time and adjust tactics automatically—if one exploitation method fails, the AI immediately tries alternatives without human attacker involvement.
The recent Akira ransomware operation exemplifies sophisticated AI cyber attacks, using AI algorithms to select victims based on revenue data and payment probability. Our incident response team has developed specific countermeasures to neutralize these AI-enhanced threats before encryption occurs.
AI cybersecurity uses artificial intelligence and machine learning to detect, prevent, and respond to cyber threats automatically without requiring human intervention for every security event. Unlike traditional signature-based security that only recognizes threats from a predefined database, AI cybersecurity platforms analyze behavioral patterns across your entire IT environment to identify both known attacks and previously unseen zero-day threats in real-time.
Modern AI cybersecurity systems process millions of security events per second, establishing behavioral baselines for every user, device, and application. When the AI detects deviations from normal patterns—such as unusual login times, abnormal data access, or suspicious process execution—it automatically alerts security teams and initiates protective responses within seconds.
Ridge IT Cyber's managed EDR services leverage AI cybersecurity platforms like CrowdStrike to achieve 98.7% threat prevention rates, detecting threats within 1 minute of execution. The technology continuously learns and adapts through cloud-based threat intelligence sharing across millions of endpoints globally, improving security daily without manual updates.
As AI-powered attacks evolve, you need to ensure your cybersecurity vendors are prepared.
Ask them:
Our Zero Trust Architecture, with AI threat detection, protects even the most complex environments against emerging AI-powered threats.
With a 245% surge in LinkedIn-based attacks, organizations need dedicated protection strategies. Start by creating clear policies for external communication, implement security awareness training focusing on social media threats, deploy solutions that can monitor message patterns across platforms, and implement browser-level protection that analyzes code execution when pages load. Teams implementing our managed security infrastructure have reported significantly improved detection rates for LinkedIn-based attacks through our multi-channel threat monitoring capabilities.
AI-generated voice technology has reached concerning levels of realism. Modern voice synthesis can create natural-sounding speech that mimics human conversation patterns, complete with natural pauses, filler words, and authentic intonation. These voices are increasingly capable of deceiving people on phone calls, particularly in high-pressure scenarios when combined with other social engineering tactics. Our clients implementing military-grade security services have found that cross-channel behavior analysis significantly improves their ability to identify these sophisticated voice-based social engineering attempts.
Traditional security tools focus on specific channels rather than analyzing the complete attack chain across multiple platforms. When attackers start with email but shift to Teams, SMS, or phone calls, your siloed security solutions miss the complete picture. Additionally, most tools don't analyze code execution when web pages load, leaving your browser—essentially an operating system—vulnerable to sophisticated JavaScript attacks. Organizations deploying The ONE Platform have consistently reported improved detection rates for these multi-channel attacks, as it provides integrated protection that follows attackers across their entire kill chain.
Attackers have developed sophisticated techniques to evade standard email security, including shifting between communication channels (email to SMS to phone), hiding malicious content in legitimate cloud apps like DocuSign, using multiple redirectors to shake off security tools, implementing "Am I Human" verification pages that block security scanners, and embedding text inside images to bypass text analysis. Our clients have found that implementing Zero Trust Architecture principles significantly improves their ability to detect these cross-channel attacks by verifying every access request regardless of which communication platform it originates from.
Black Basta has developed a sophisticated attack method using AI to sign victims up for hundreds of legitimate newsletter subscriptions, overwhelming their inbox for 30-90 minutes. This creates confusion and frustration, after which attackers contact targets through Teams messages or spoofed phone calls, impersonating IT support and offering to "fix" the email problem. Once victims download the supposed fix, their systems become compromised with ransomware. Organizations that trust us as their MSSP benefit from advanced frequency pattern analysis that detects and blocks these psychological smokescreens before they can establish a foothold in your environment.
Unlike large language models that require massive infrastructure, attackers are shifting to Small Learning Models (SLMs) that can run on a single gaming PC. This means they don't need data centers—they can operate completely anonymously using just a computer with a high-end graphics card like an NVIDIA 4080. These specialized AI models can be trained for specific attack tasks, chain together for complex operations, and operate with minimal footprint. Many of our clients have found that The ONE Platform's distributed AI detection capabilities provide the visibility they need across their entire messaging landscape to identify these emerging threats.
Inc. Magazine's fastest growing leader in Managed Cybersecurity—3 years in a row.
Rapid response times, with around the clock IT support, from Inc. Magazine’s #1 MSSP.
Rapid response times, with around the clock IT support, from Inc. Magazine’s #1 MSSP.